
Law or order? “Cl0p” Ukraine-based hacking group in an international intrigue
The “Cl0p” Ukraine-based hacking group still seems active despite the country’s tragic ongoing warfare. And despite a massive law enforcement operation in the Kyiv region in June 2021 by the Ukrainian cyber police, involving authorities from the US, South Korea and Interpol.
During that operation, six alleged members of the group were arrested for “Unauthorized interference in the work of computers” and “Legalization (laundering) of property obtained by criminal means”. The agents seized computer equipment, cars, and about 5 million hryvnias (Ukrainian currency).
Yet, the group continues to operate. The last antivirus scan of a Cl0p-related file dates back to April 2022. According to the Japanese cybersecurity company “Trendmicro“, Cl0p detections have been more than 350 in January 2022.
“The fact that the group survived that scrutiny and is still active indicates that the main members were not caught in those raids”, Lior Div (CEO and co-founder of cybersecurity company “Cybereason”) wrote in December. Why is it so difficult to stop their activity?
Cl0p, a cyber investigation on a ransomware group

Summary of contents
Ransomware and the gang
“Cl0p” is the initial name given to a malicious software family. It comes from the letters attached at the end of the filenames involved in the hacking (their extension): “.Clop”. According to “Cybereason”, the name “clop” comes from Russian or Bulgarian and means “bug”.
In 2019, security experts discovered the use of “Cl0p” by a well-known cybercriminal group named “TA505” when it launched a phishing campaign.
The hackers sent a tricky email with malicious files to the mailboxes of company employees. After opening the infected file, the malware (abbreviation for malicious software) downloaded additional programs and completely infected the victim’s computers (and often the entire network) through remote management. Then, the cybercriminals encrypted the company’s data and asked for a ransom to decrypt them.
The name “Cl0p” also designates the gang using this malware for extortion. It is called “ransomware” because it leads to the request for a ransom. According to Cybereason, ransomware is “a malicious software designed to block access to a computer system or computer files until a sum of money is paid”.
South Korea and the US
The Ukrainian police statement, released after the 2021 operation, informed that the cybergang Cl0p encrypted data from South Korean and US entities.
In 2019, Cl0p attacked four South Korean companies: 810 internal servers and employees’ personal computers were blocked. The cybercriminals received a “ransom” in cryptocurrency for restoring access.
In 2021, the suspects had encrypted employees’ data and financial reports of US universities: Stanford University Medical School, the University of Maryland and the University of California.
The total losses reached $500 million as of June 2021, the Ukrainian police reported.
The double extortion
Not paying the ransom becomes more and more difficult. In various attacks, the Cl0p hackers not only demanded money to restore access. In case of non-payment, they threatened to disclose the confidential data of the victims. Indeed, the criminals began to exfiltrate it before the encryption.
It is the “double extortion” tactic because of the two steps of the threat:
1) block access to the files;
2) expose the victims’ files publicly.
This blackmail is now “a mainstream practice”, Mrs Tine Munk (Lecturer in Criminology at Middlesex University) wrote in her 2022 book “The rise of politically motivated cyber attacks“.
According to TrendMicro, “the operators behind Cl0p made their first attempt at using the double extortion scheme in April 2020 when they publicized the data of a pharmaceutical company”.
The Dark Web portal

Cl0p Portal Frontpage
If the victim doesn’t pay the ransom, the cybercriminals expose the leaked files on their dark web portal: ‘CL0P^-LEAKS’.
Indeed, Cl0p published a list of the targetted entities which didn’t accept the conditions of the gang. Each has a page with
1) the communications maintained by the hackers with the victims;
2) the documents leaked during the attack (including contacts, names and even passport scansions).
The disclaimers and the copycats
The portal of the gang contains some alerts, too.
A disclaimer states that the group have never attacked hospitals, orphanages, nursing homes, or charitable foundations, and they “will not” (commercial pharmaceutical companies are not listed). “If an attack mistakenly occurs on one of the previous organizations”, – they said – “we will provide the decryptor for free, apologize and help fix the vulnerabilities”.
Still, according to TrendMicro enquiry, published on the 22nd of February 2022, the healthcare “sector received the highest number of detections [of Cl0p attempts] at 959, followed by the financial industry at 150“.
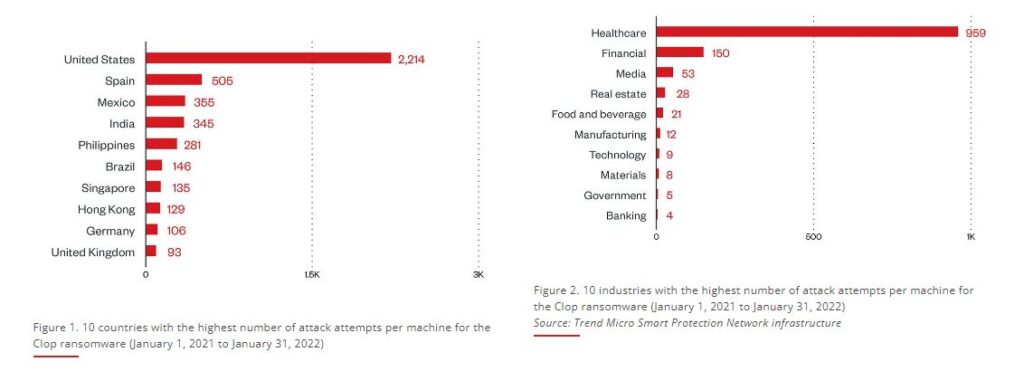
TrendMicro – Cl0p targeted sectors
However, the Cl0p hackers specified on their portal that there are imitators. “We get reports of people attacked by criminals who say they are Cl0p. This is not true and these are just copycats who know nothing of us. (…) Cl0p will only communicate through our official email or web chat”.
There is a warning at the bottom of the page followed by a smiley face: “Cl0p^_-LEAKS 2020-2022. All rights reserved ;)”. 2022 is the most recent year of their activities.
Cl0p is still active
The activities seem ongoing, according to an investigation, too.
Hybrid Analysis
Hybrid-Analysis.com is “a free malware analysis service that detects and analyzes unknown threats”. Querying the name “Clop”, the website returns the details of some malicious files.
One of them, with submission names “clop.bin” or “11hgfgh.exe” (labelled as malicious), dated the last antivirus scan on the 17th of April 2022.
Any.run
Additional information comes from any.run, a website providing an interactive malware-hunting service.
According this latter service, the file named “clop.bin” or “11hgfgh.exe”, identified by a unique “digital fingerprint” left by the malware (SHA-256: a867deb1578088d066941c40e598e4523ab5fd6c3327d3afb951073bee59fb02) is related to several files with extension name “.clop”.
Virus Total
Another special tool to investigate malware is VirusTotal. It is a website aggregating scan engines and antivirus results to give the malicious software queried profile.
The same file (“clop.bin” or “11hgfgh.exe”), researched through its fingerprint, was last seen on the 18th of May 2022, according to VirusTotal.
The Ukrainian-based group seems to be still operative. And prolific.
The number of detections
According to TrendMicro analysis, Cl0p operations have remained robust as the number of detections consistently straddled monthly in the 300 to 400 range from July 2021 to January 2022.
The quantity is impressive. Of course, the group alerts on possible “copycats”. These statistics could feel the effect of these.
However, TrendMicro gave another explanation for the high levels of detection. “Cl0p is an example of ransomware as a service (RaaS)“.
US company Crowdstrike defined RaaS as “a business model between ransomware operators and affiliates in which affiliates pay to launch attacks developed by operators.” In return, the operators receive a percentage of the victim’s ransom.
The operators could have rules of engagement. Yet, it is challenging to identify the actual attackers, why, and from where they decide the attacks.
Cl0p members’ base
Some declarations informed that Cl0p could not be mainly based in Ukraine, where the cyber police executed the June 2021 operation.
After the raid, Andras Toth-Czifra, senior analyst at cybersecurity company “Flashpoint”, which had been tracking Cl0p’s activities, suggested (in an interview with the website DarkReading) that Cl0p could be “situated in Russia”.
Cybersecurity intelligence firm “Intel 471” told the website KrebsonSecurity on the operation: “We do not believe that any core actors behind CLOP were apprehended because they are probably living in Russia”.
In December 2021, Cybereason wrote that Clop hackers “are most likely based in Russia —which has a history of tacitly supporting cybercriminals with state-condoned and state-ignored attacks “.
Russia, the “one rule” of hacking

Russia under the mag glass
Mrs Tine Munk explained Russia’s policy regarding hacking groups. She wrote in 2022 that “the rationale behind the growing number of attacks originating from Russia is the “one rule” of Russian hacking. The ransomware groups [in Russian Federation] can attack anyone as long as the attack is not launched on friendly soil”.
“As long as the ransomware groups leave Russia” and select other countries, Munk continued, “they can do whatever they want to and make money the way it suits them”.
International law, the UN and the NATO
The situation poses an issue with international law and States’ relationships. Indeed, two UN distinct groups are working on the applicability of existing international law in cyberspace: the Governmental Group of Experts (GGE) and the Open-Ended Working Group (OEWG).
The problems are still a lot.
Sometimes the government don’t respect their engagement. According to a NATO Parliamentary assembly report (published on the 4th of April 2022), “the surge in ransomware attacks has highlighted the role of states that tolerate criminal groups on their territory, despite their commitments”.
Moreover, sometimes the positions of the states are not unanimous. Following some guidelines by UN working groups, France and Netherlands “want the recognition of a mandatory due diligence rule for cyberspace. (…) States would have a duty to ensure that neither their territory nor their cyberinfrastructure is being used to carry out cyber-attacks”, the NATO assembly pointed out. But several governments, including the Russian and Chinese ones, opposed it.
Profits or politics
“According to the Kremlin, Russian law does not have provisions to prosecute the ransomware attacks on foreign soil”, Munk wrote. But are they common crimes or international policy issues? The evaluation is not easy.
Cl0p actors appear to be profit-driven cybercriminals. MITRE ATT&CK, an accessible knowledge base of adversary tactics and techniques, describes the group TA505 (behind Cl0p malware) as “a financially motivated threat group that has been active since at least 2014″. Is it so?
The countries targeted
The countries most targeted by Cl0p can give an overview of the gang’s objectives. Indeed, as of the 23rd of May, the leaked files in the portal “CL0P^-LEAKS” regard 111 entities.
72 of them have their headquarters in the US;
9 in Germany;
8 in Canada;
7 in the UK;
2 each in India, South Korea, Singapore, and Switzerland;
1 each in Japan, France, Australia, Malaysia, and Italy;
2 also in China: the hackers accused these latter of stealing “USA company technology (…) Cl0p make bad corporations pay for their crime – they explain – even when a corrupt government does nothing”.
Profits and politics are not so distant. “The ransomware groups are not operating on the request of Russia, but with the tactical acceptance of Russian strategies” in terms of targets’ selection, Mrs Munk stated in her 2022 book.
They often blur the lines between financially motivated attacks and political targets. What to do?
International law is not a golem

The Kremlin
International law is not a “golem” created once and immutably. It is a process, and agreements between states often come before an endorsed rule.
During a summit in Geneva in 2021, US president Joe Biden and Russia’s President Vladimir Putin agreed to develop a cybersecurity arrangement between the two countries.
However, according to Munk, although the US and Russia consented to do something about the surge in cyberattacks, particularly ransomware, “it remains uncertain if the Russian authorities will take action on these matters”.
The Russian invasion of Ukraine didn’t help. On the 7th of April, Oleg Khramov, Deputy Secretary of the Security Council of the Russian Federation, told the newspaper “Rossiyskaya Gazeta” that Washington closed a communication channel with Russia on cybersecurity issues.
Indeed, he said that in February, Moscow offered the US to cooperate to protect the critical infrastructure of both countries. “The White House has notified us that it is unilaterally withdrawing from the negotiation process”, Khramov said in April.
A long path for a shared law is still to come.








